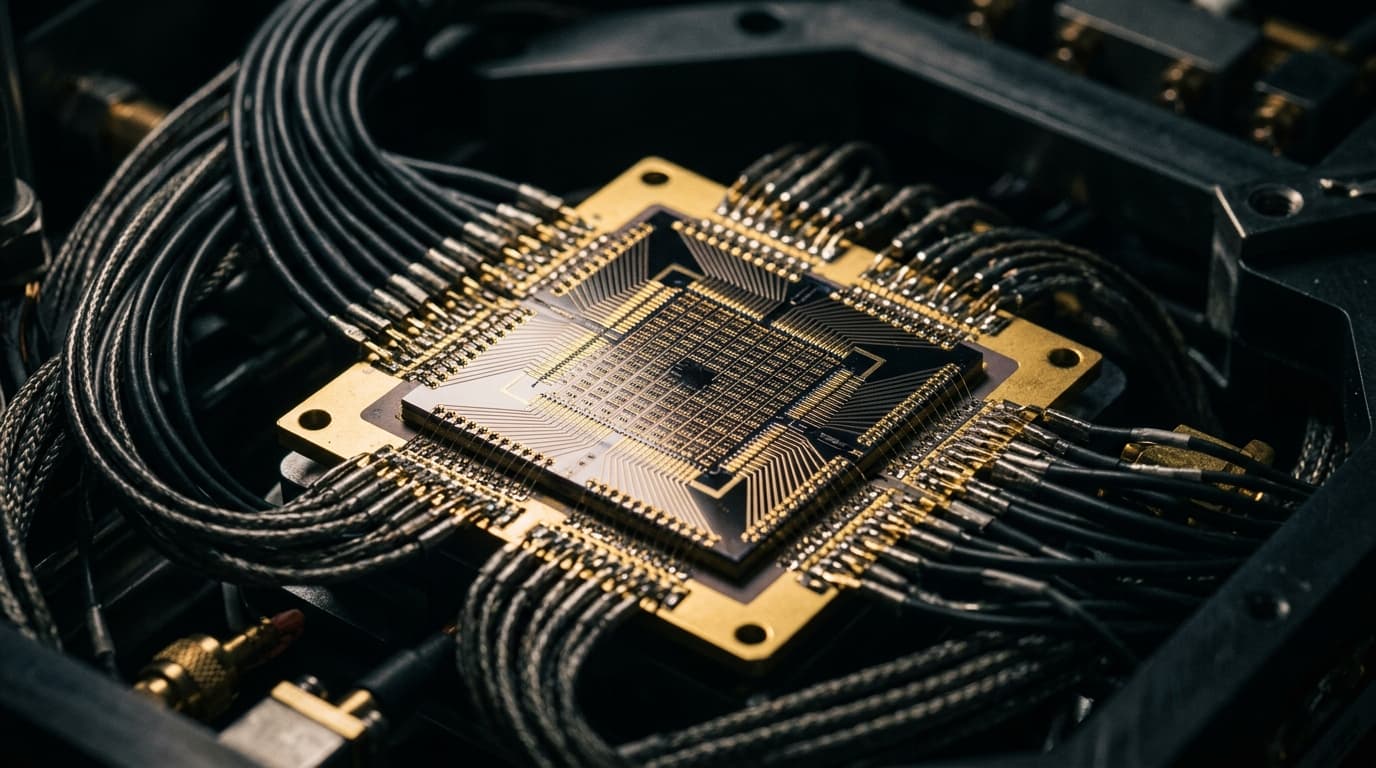
Google's Quantum Computer Claims It Could Crack Bitcoin in 9 Minutes, But Here's the Full Story
Google's whitepaper claims quantum computers could break Bitcoin's cryptography in 9 minutes. Here's what's real, what's hype, and what you should do.
A 9-minute Bitcoin hack sounds terrifying. That's the headline-grabbing claim from Google Quantum AI's March 2026 whitepaper, which estimates a future quantum computer could derive a private key from an exposed public key in about nine minutes, potentially hijacking transactions before they confirm.
But before you panic-sell or start memorizing seed phrases in dead languages, the full picture is considerably more nuanced. The threat is real but not imminent, and the cryptocurrency industry has time to adapt, provided it actually does so.
What Google Actually Said
Google's whitepaper, published March 31, 2026, describes a theoretical attack on Bitcoin's ECDSA (Elliptic Curve Digital Signature Algorithm) cryptography. The key finding: a fault-tolerant quantum computer could break ECDLP-256 using fewer than 500,000 physical qubits. That's a 20-fold reduction from previous estimates of around 10 million qubits.
The "9-minute hijack" scenario works like this: When you broadcast a Bitcoin transaction, your public key becomes visible in the mempool for roughly 10 minutes before the transaction confirms. A quantum attacker with sufficient hardware could theoretically derive your private key from that public key in about 9 minutes, with approximately a 41% success probability, then broadcast a competing transaction to steal your funds.
That's a genuine vulnerability. It's also entirely theoretical right now.
The Hardware Gap Nobody's Talking About
Here's what the breathless headlines often skip: Google's most advanced quantum computer, Willow (announced December 2024), has 105 qubits. The attack described in their whitepaper requires fewer than 500,000 qubits, which sounds like progress, but we're still talking about a roughly 4,700x increase from current capabilities.
Some researchers have historically estimated that breaking ECDSA would require around 1.9 billion qubits using older techniques. Google's new estimates are dramatically more efficient, but "more efficient" and "currently possible" are very different things.
No cryptographically relevant quantum computer (CRQC) exists today. Period.
The Real Exposure Problem
That said, the long-term concern is legitimate. Approximately 6.9 million BTC (around $470 billion at current prices) sits in legacy addresses with exposed public keys. This includes an estimated 1.7 million coins from the Satoshi era that have never moved.
Ironically, Bitcoin's 2021 Taproot upgrade, designed to improve privacy and efficiency, actually increased quantum exposure by defaulting to public key representation in certain transaction types.
This creates a genuine "harvest now, decrypt later" risk. An adversary could theoretically collect encrypted data today and wait for quantum computers capable of breaking it. For high-value Bitcoin holdings, that's worth considering.
What the Industry Is Doing
Google has moved its internal migration to post-quantum cryptography (PQC) deadline to 2029, and they're urging cryptocurrency networks to follow suit through soft or hard forks.
Ethereum is leading the response with its 2026 "Glamsterdam" upgrade, incorporating PQC via zero-knowledge proofs. Justin Drake, a prominent Ethereum researcher, estimates a 10% chance of quantum key recovery by 2032, which is low but not negligible for a $470 billion exposure.
Bitcoin's decentralized governance makes rapid upgrades harder. BTQ Technologies' Chris Tam warns that meaningful upgrades could take years and potentially require contentious forks like a hypothetical "Bitcoin Quantum" chain.
The Counterargument Worth Hearing
Some security researchers call the "9-minute hack" framing overblown. Critics note that coverage often conflates Willow's benchmark achievements with unrelated ECDSA cracking capabilities, creating a misleading impression of imminent danger.
The mempool timing attack, while theoretically elegant, also assumes an attacker has both a quantum computer capable of the math and the infrastructure to reliably front-run transactions on the Bitcoin network. That's a lot of assumptions stacked together.
The threat is real in the same way asteroid impacts are real: worth preparing for, not worth panicking about today.
Practical Steps for Bitcoin Holders
While quantum-resistant Bitcoin wallets don't exist yet, you can reduce exposure with sensible practices:
Don't reuse addresses. Every time you spend from an address, you expose your public key. Fresh addresses for each transaction minimize this window.
Consider cold storage seriously. Services like River offer full-reserve custody with proof of reserves, which matters more as potential attack vectors multiply. Their institutional-grade security and U.S.-based support provide a meaningful layer between your holdings and emerging threats.
Watch for protocol upgrades. When Bitcoin does implement post-quantum cryptography, you'll likely need to migrate funds to new address types. Staying informed beats scrambling later.
Privacy matters more now. Tools like Cashu.me, which uses ecash for private Lightning transactions, help minimize the public exposure of your transaction patterns. Less visible means less targetable.
The Timeline That Actually Matters
The honest assessment: quantum computers capable of breaking Bitcoin's cryptography are probably 5-15 years away, depending on who you ask and how optimistic they are about error correction advances.
Bitcoin's upgrade cycle is slow but not frozen. The network has successfully implemented significant changes before (SegWit, Taproot), and the quantum threat provides strong motivation for the next evolution.
The 2029 deadline Google has set for its own PQC migration is a reasonable benchmark. If a major tech company is treating that as urgent, cryptocurrency networks should probably match that pace.
What This Means Going Forward
Google's whitepaper isn't a fire alarm; it's a smoke detector going off in a building where the fire is still several floors away. The appropriate response is orderly preparation, not panicked evacuation.
The Bitcoin network will need to evolve. That evolution will probably be contentious, slow, and imperfect. But it's also possible, and the alternative (ignoring the threat until it's acute) would be far worse.
For individual holders, the actionable takeaway is boring but true: use good security practices, don't reuse addresses, diversify custody approaches, and stay informed about protocol developments. The quantum threat adds urgency to advice that was already sound.
Nine minutes is a scary number. But we have years to prepare, and preparation beats panic every time.