Google's Quantum Computer Could Crack Bitcoin in 9 Minutes and What That Means for Your Holdings
Google's March 2026 research shows quantum computers could break Bitcoin keys in 9 minutes. Here's what the threat timeline actually looks like.
Nine minutes. That's how long Google Quantum AI estimates a sufficiently powerful quantum computer would need to derive a Bitcoin private key from its public key, according to research published on March 31, 2026. The finding has reignited debate about cryptocurrency's long-term security, though the reality is more nuanced than the headline suggests.
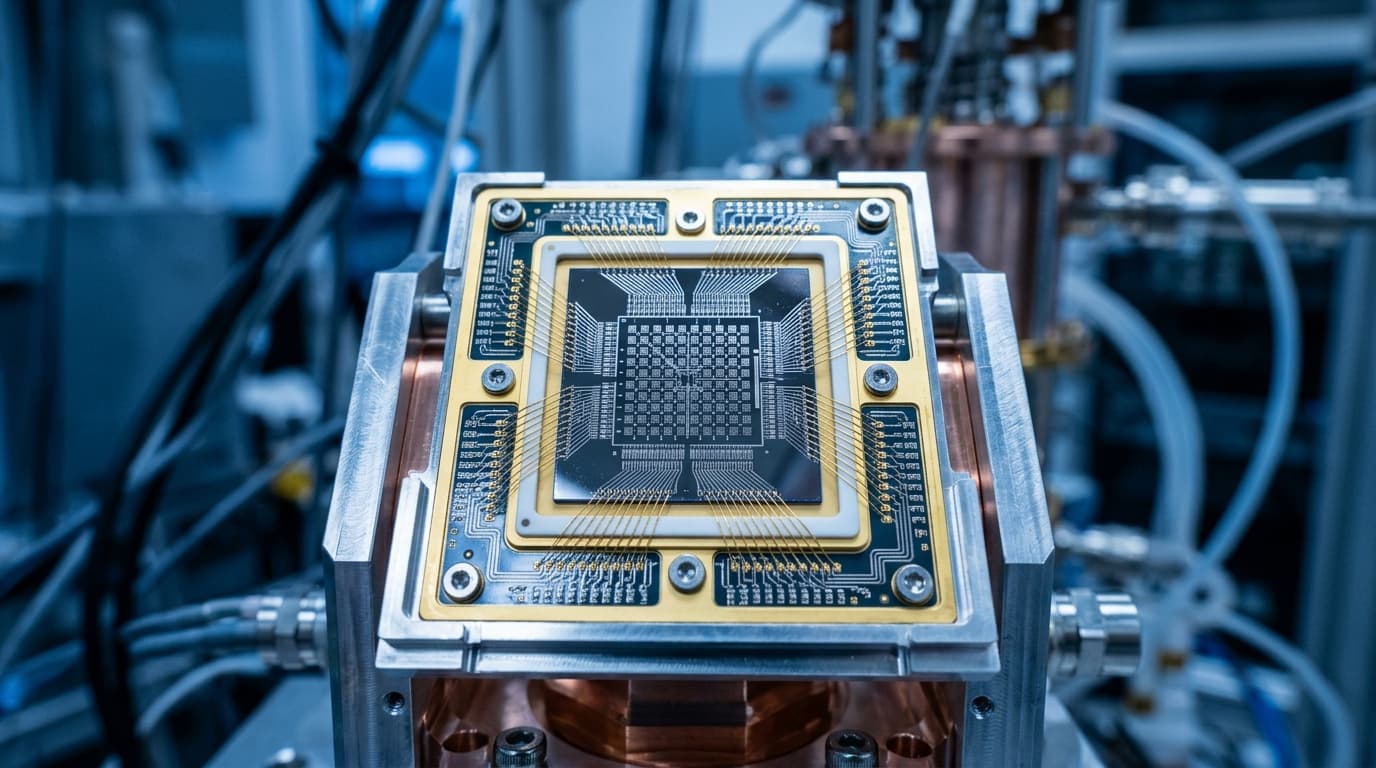
The Google whitepaper details how a superconducting quantum computer with fewer than 500,000 physical qubits could break Bitcoin's ECDLP-256 cryptography using an optimized version of Shor's algorithm. That's a significant reduction from previous estimates that assumed millions of qubits would be necessary.
What the Research Actually Shows
Google's analysis focuses on what researchers call "on-spend attacks." When you send Bitcoin, your public key briefly becomes visible on the network before the transaction confirms. A quantum computer fast enough could theoretically derive your private key during that window and submit a competing transaction.
The math isn't reassuring: Google estimates roughly 41% success probability before Bitcoin's typical 10-minute confirmation time. The attack wouldn't work against addresses that have never sent funds, since their public keys remain hidden behind cryptographic hashes.
Here's where things get concrete. Approximately 6.9 million BTC sits in vulnerable addresses with exposed public keys. That includes Satoshi-era P2PK outputs, reused addresses, and some Taproot configurations. At current prices, that's around $150 billion in potentially exposed funds.
A separate paper from Caltech and Oratomic, published concurrently, suggests even fewer resources might be needed. Their estimate: roughly 10,000 qubits could crack the same cryptography in 10 days. That represents a 20-fold reduction in qubit requirements compared to estimates from just a few years ago.
No Imminent Threat, But a Shrinking Timeline
Before panic sets in, some perspective: no quantum computer currently exists that poses this threat. Google's Willow chip demonstrated verified quantum advantage in 2024-2025, but commercial cryptographically-relevant quantum computers (CRQCs) remain years away.
Google has moved its recommended post-quantum cryptography migration timeline to 2029, urging blockchain networks to begin transitions now. The Ethereum Foundation, which co-authored the Google paper, has adopted the same target date.
Not everyone agrees the timeline is accurate. Some analysts argue quantum risk remains overhyped, partly for marketing purposes, and don't expect a practical break before 2035 or later. Chris Tam of BTQ Technologies takes the opposite view, warning that network upgrades require months or years of coordination, making 2029 an aggressive target.
Why Ethereum Has More Breathing Room
Ethereum transactions face lower risk from on-spend attacks due to faster confirmation times. The public key exposure window is simply shorter, making the race between quantum decryption and network confirmation less favorable for attackers.
This doesn't mean Ethereum is immune. Both networks rely on the same underlying cryptographic assumptions that quantum computers threaten. But it does suggest Bitcoin's longer block times create specific vulnerabilities worth addressing.
What You Can Do Today
The most immediate protection is straightforward: don't reuse addresses. Each time you send Bitcoin from an address, you expose its public key. Using fresh addresses for each transaction keeps your remaining funds protected behind hash functions that quantum computers can't easily break.
For larger holdings, multisignature setups add meaningful protection. An attacker would need to compromise multiple keys rather than just one, significantly raising the difficulty of any attack. Bitcoin Keeper offers multisig vault configurations (like 2-of-3 or 3-of-5) that distribute risk across multiple keys and devices, providing a buffer against single points of failure, quantum or otherwise.
Hardware wallets with air-gapped signing add another layer. By keeping private keys offline and using devices like Coldcard with a coordination layer like Bitcoin Keeper, you minimize exposure to both conventional and future threats.
The Longer View
The crypto industry will eventually need to migrate to post-quantum cryptographic standards. This isn't optional. The question is timing and coordination.
Some proposals already exist. BTQ Technologies has suggested quantum-safe forks, including a concept called Bitcoin Quantum. Whether the Bitcoin community would adopt such changes, given its historically conservative approach to protocol modifications, remains uncertain.
Google's paper recommends zero-knowledge proofs for responsible disclosure of vulnerabilities, a way to prove a quantum break is possible without actually exploiting it. This could provide early warning and time for coordinated response.
Balancing Preparation and Perspective
The honest assessment: quantum computers won't steal your Bitcoin tomorrow, but the timeline for potential threats has compressed significantly. Google's research suggests the window for preparation is measured in years, not decades.
For most holders, sensible practices, such as avoiding address reuse, using multisig for significant holdings, and staying informed about protocol developments, provide reasonable protection during this transition period. The technology to break Bitcoin doesn't exist yet. The technology to protect against it when it does is already available.
What changes is urgency. Three years ago, quantum threats felt theoretical. Today, major research institutions are publishing specific timelines and resource estimates. The prudent response isn't panic; it's preparation.